- It appears that there is an issue in taint propagating RemoteFlowSource if it goes through InputSource + StringReader constructors , not sure if that is intentional or not because it's missing some valid flows.
I have an example vulnerable code (https://github.com/JoyChou93/java-sec-code/blob/master/src/main/java/org/joychou/controller/XXE.java#L47-L50)
String body = WebUtils.getRequestBody(request);
logger.info(body);
XMLReader xmlReader = XMLReaderFactory.createXMLReader();
xmlReader.parse(new InputSource(new StringReader(body))); // parse xml
return "xmlReader xxe vuln code";
This normally should be flagging as valid XXE vulnerability , however it's not with the normal XXE taint configuration.
If we add the following hack-y taintstep , the vulns will be flagged
override predicate isAdditionalTaintStep(DataFlow::Node pred, DataFlow::Node succ) {
exists(MethodAccess m | m.getAnArgument() = pred.asExpr() and succ.asExpr() = m)
}
Default XXE config : no findings

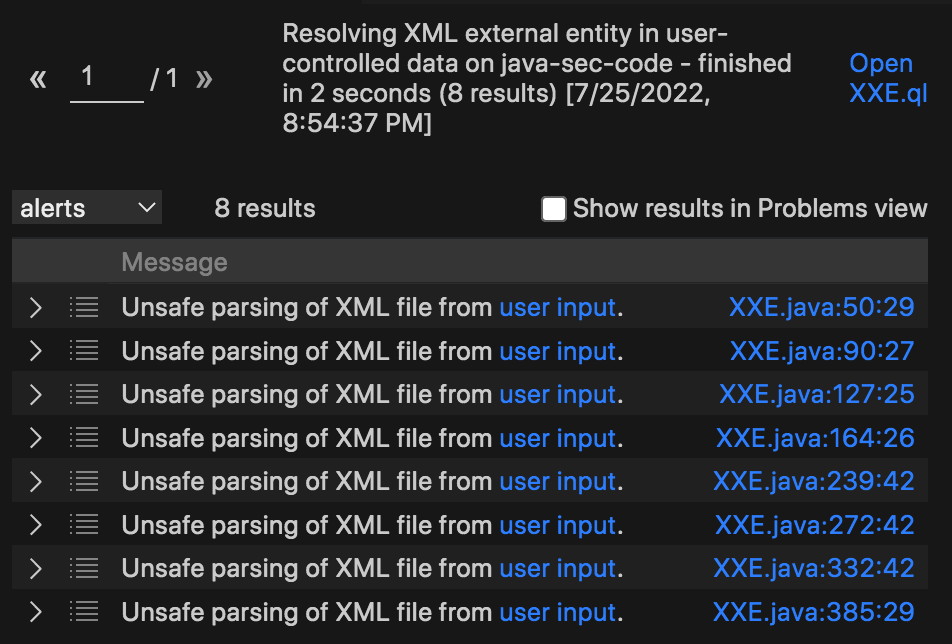
After taint step :
I have an example vulnerable code (https://github.com/JoyChou93/java-sec-code/blob/master/src/main/java/org/joychou/controller/XXE.java#L47-L50)
This normally should be flagging as valid XXE vulnerability , however it's not with the normal XXE taint configuration.
If we add the following hack-y taintstep , the vulns will be flagged
Default XXE config : no findings

After taint step :